Make the worldquantum safe
Secure your enterprise for the quantum era
Quantum computers are scaling rapidly. Soon, they will be powerful enough to solve previously unsolvable problems. This opportunity comes with a global challenge: quantum computers will be able to break some of the most widely-used security protocols in the world.
Quantum-safe software solutions
IBM Quantum Safe Explorer
Scan applications to discover cryptographic artifacts and vulnerabilities. Create various cryptographic inventory reports, including a Cryptography Bill of Materials (CBOM).
IBM Quantum Safe Advisor
Create a dynamic cryptographic inventory to guide remediation. Observe and analyze cryptographic posture and compliance to prioritize risks.
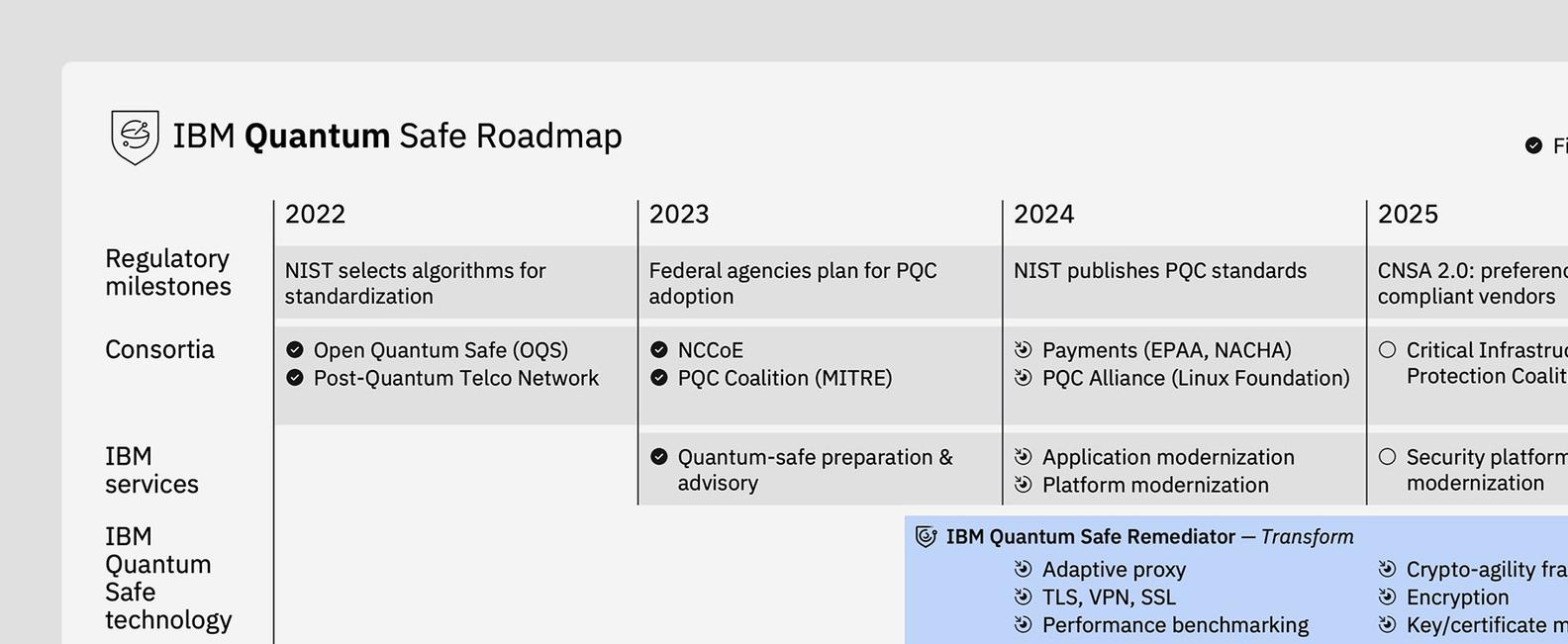
IBM Quantum Safe Remediator
Learn and apply best practices for quantum-safe remediation patterns. Build crypto-agility through automated and human-assisted solutions as you transform your cryptography.
Build on quantum-safe infrastructure
IBM z16™
IBM Cloud®
Your roadmap to quantum-safe readiness
Case studies
IBM Quantum Safe x Vodafone
IBM and Vodafone have partnered to secure telecom for the quantum computing era
Watch the video
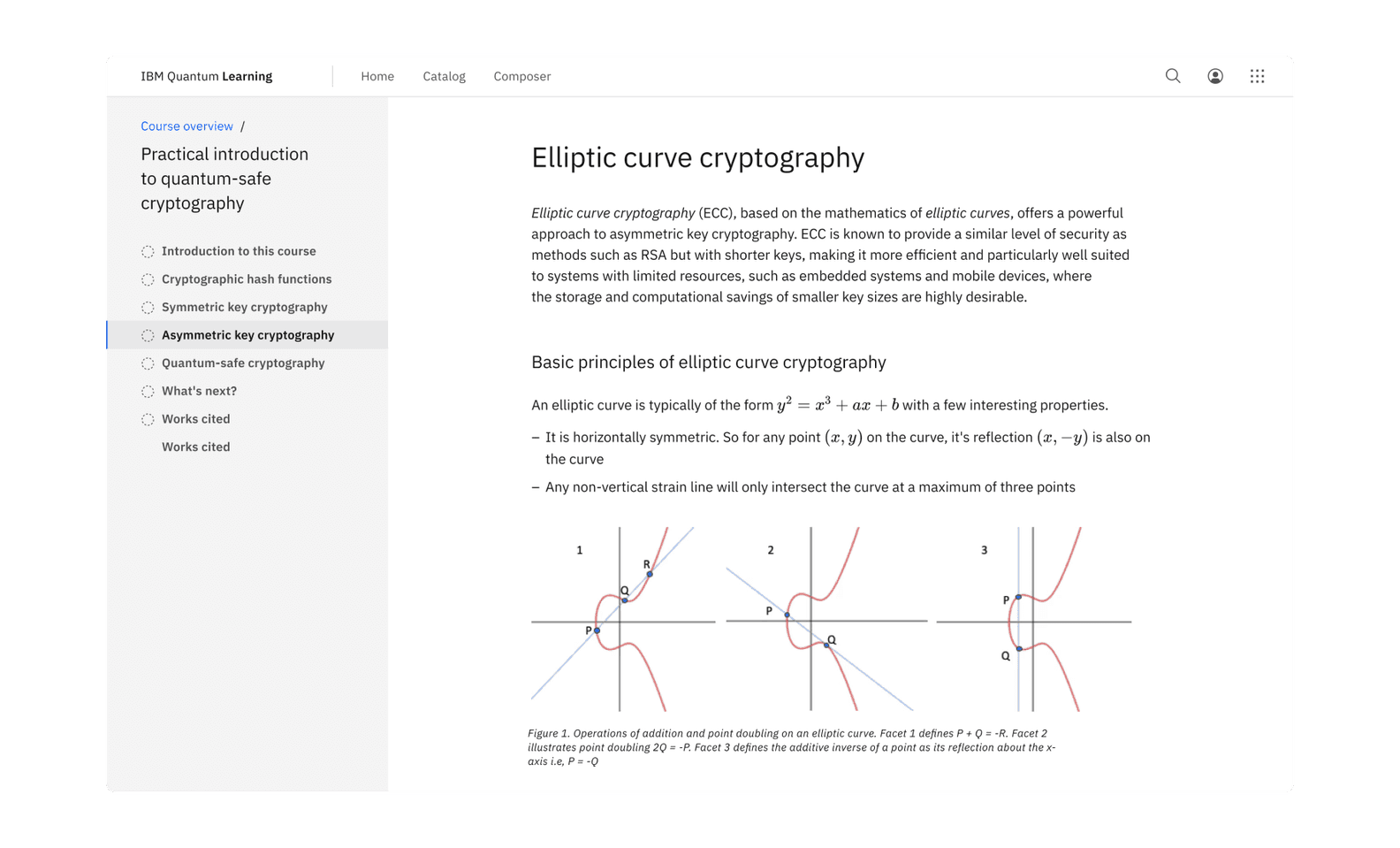
Learn the basics of quantum-safe cryptography
Build proficiency in quantum-safe cryptography with free hands-on labs and interactive lessons.