How To
Summary
This document explains the benefits, setup, and configuration that is needed to integrate the Zscaler ZIA solution with the MaaS360 Threat Management service. To enable this feature, customers must have an active subscription to Zscaler solutions.
Objective
- Enhanced phishing detection
MaaS360 has partnered with Zscaler to enhance phishing detection and enforcement capabilities on mobile devices. MaaS360 can warn users ahead of time that they have received malicious links in an SMS text or in an email message. With Zscaler, users can block malicious links at the time of access. Phishing detection and enforcement also applies to all apps that are installed on a device. - Unified dashboard that displays threat events that occur on a device
MaaS360 administrators can view threat detections that occur across both Zscaler and MaaS360 in a common dashboard. All phishing events are labeled with the "Malicious URLs Accessed" risk name. Administrators can access each risk incident to view the devices and users that are affected by the phishing event.
- Aggregated device risk score
When a risk score is computed for a device, the risk score now includes the new "Malicious URLs Accessed" risk type. The device risk score is not only based on events that are generated from MaaS360, but also includes threat detections from Zscaler. By correlating data from multiple systems, this computed risk score is a more accurate representation of device security posture. This value is a significant indicator to identify risky devices and apply stricter policies. - UEM device context for all threat events that originate from mobile devices
Most XDR platforms are limited to what actions can be taken on mobile devices since they lack the information that is needed to uniquely identify the device. Due to privacy restrictions, most OS vendors prevent applications from accessing device information that is needed to accurately identify a device.
By enabling the Zscaler integration with MaaS360, all Zscaler threat events include additional information that is needed to uniquely identify a device. These events also provide additional information that accurately represents device security posture such as device risk score and user risk score. Administrators can use this information to automate or manually take actions that improve the security posture of the device.
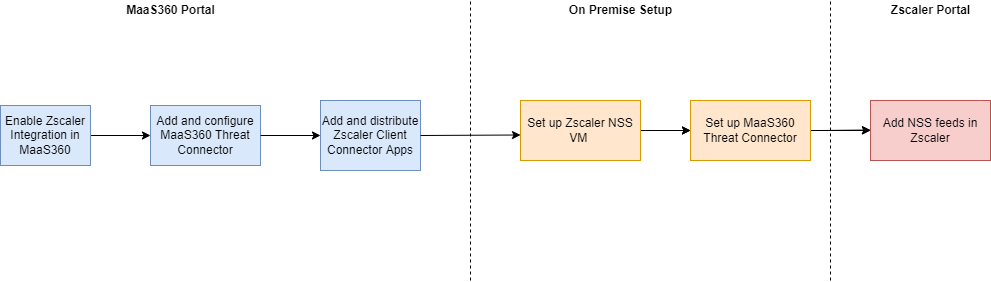
Steps
- Enabling the service from the MaaS360 Portal: Threat Management Services > Endpoint Security Service
- Enabling the MaaS360 customer property: Contact IBM MaaS360 support to enable the Enable Zscaler Integration customer property.
- IBM MaaS360 Support must also add an access role for an administrator to configure the Zscaler integration.
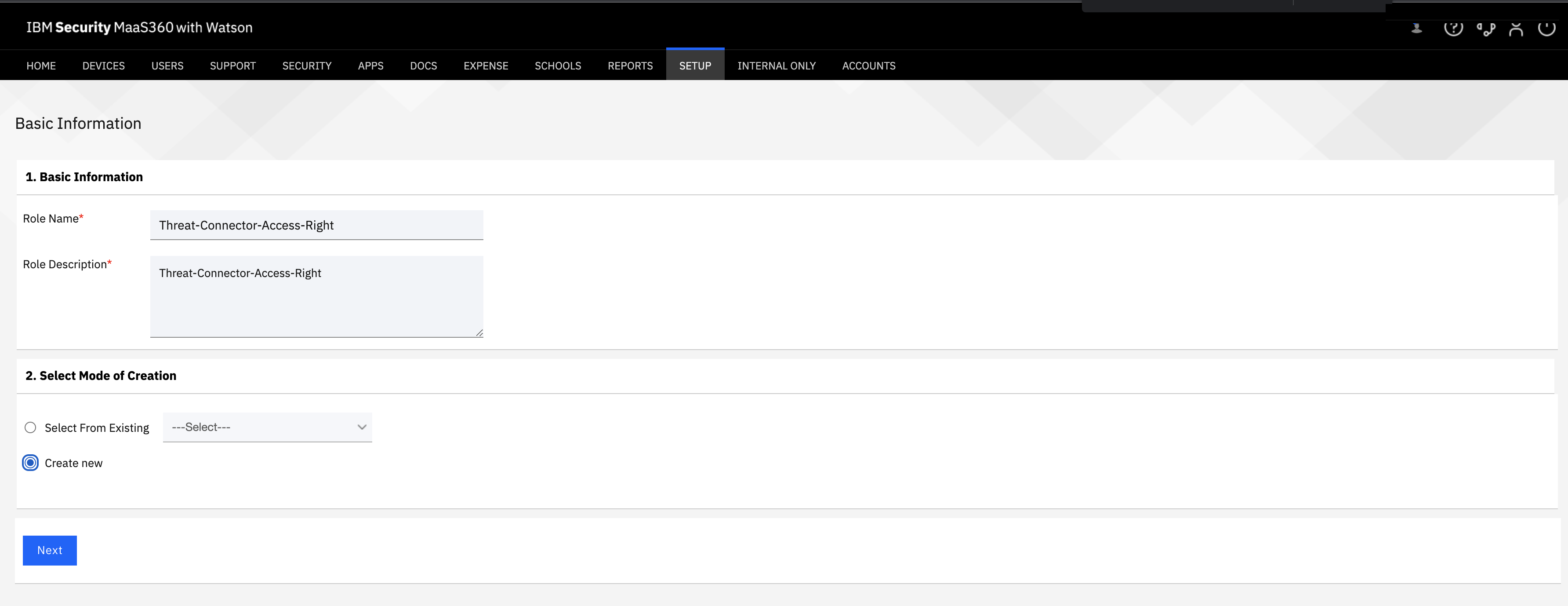
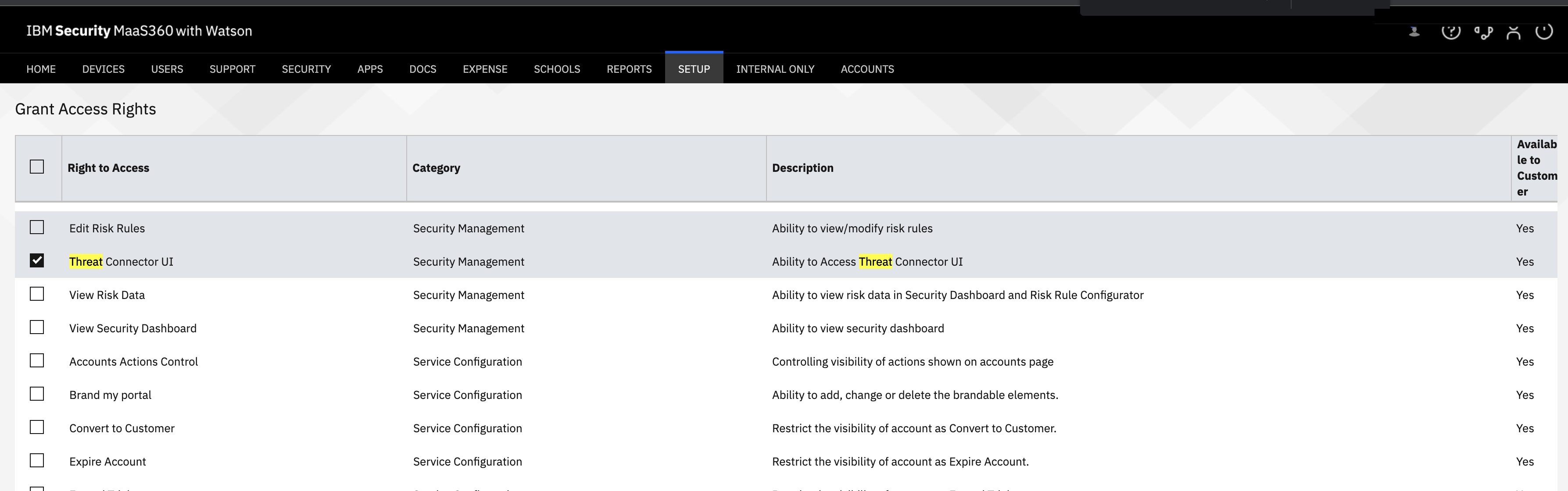
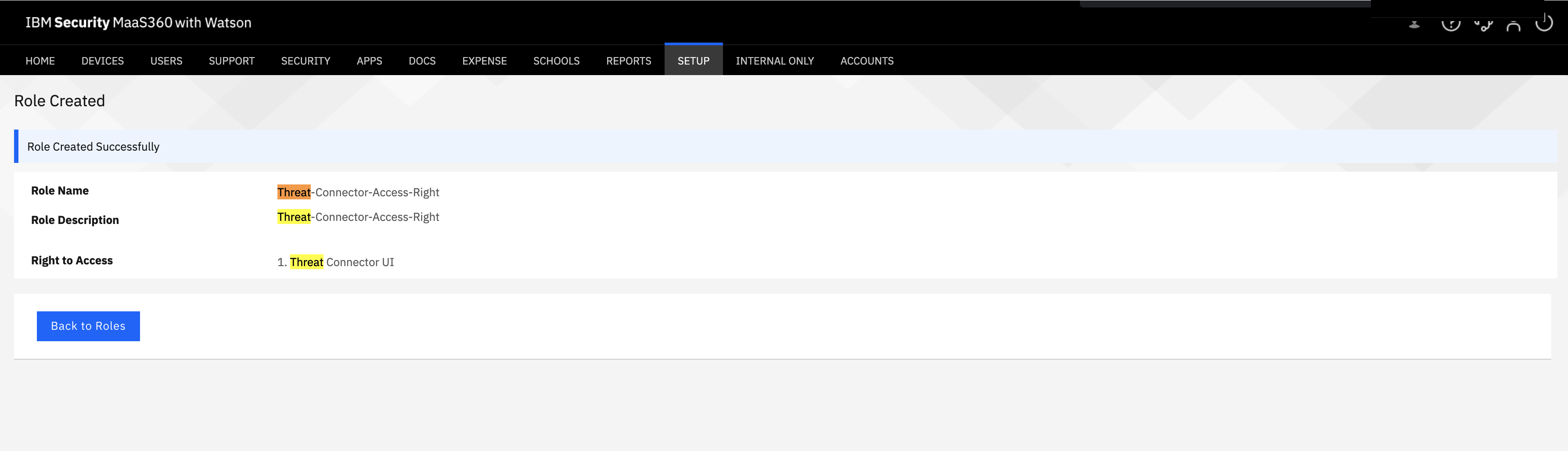
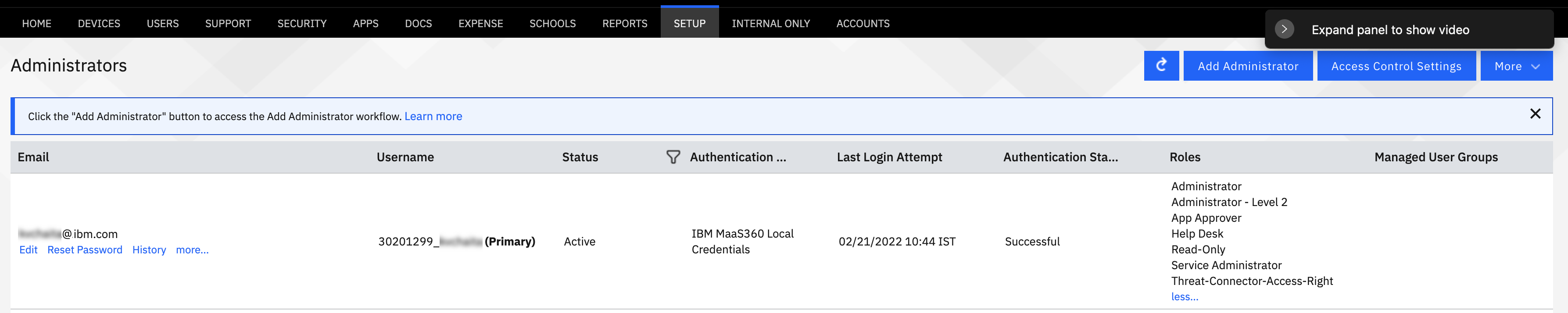
- MaaS360 administrator role changes: You must create a new role for administrators to add and manage threat connectors that integrate with Zscaler. The following screen captures depict how to create the role:
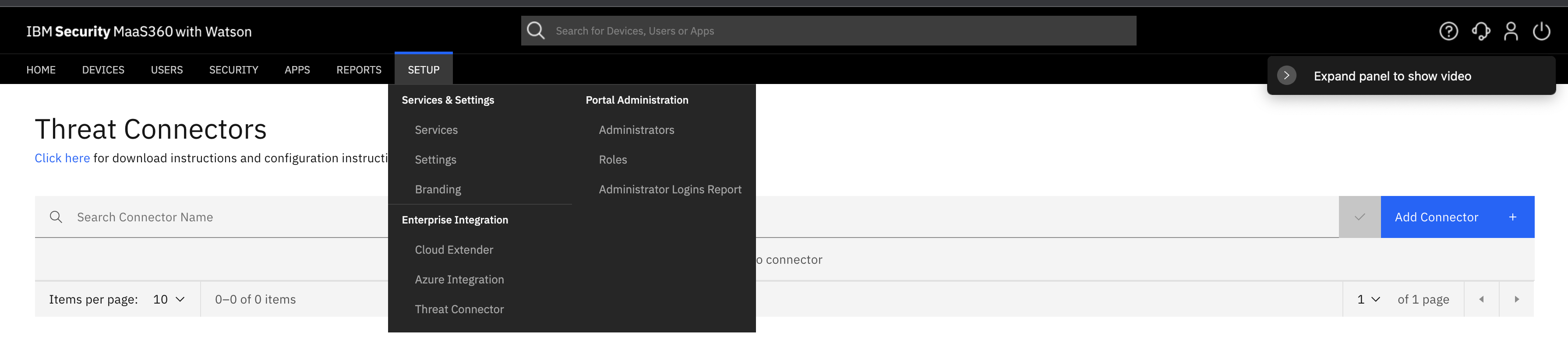
- Go to Setup > Threat Connectors.
- Click Add Threat Connector.
- Enter a unique name and description for the threat connector.
- Select Zscaler as the threat vendor.
- Click Validate Details, and then click Next.

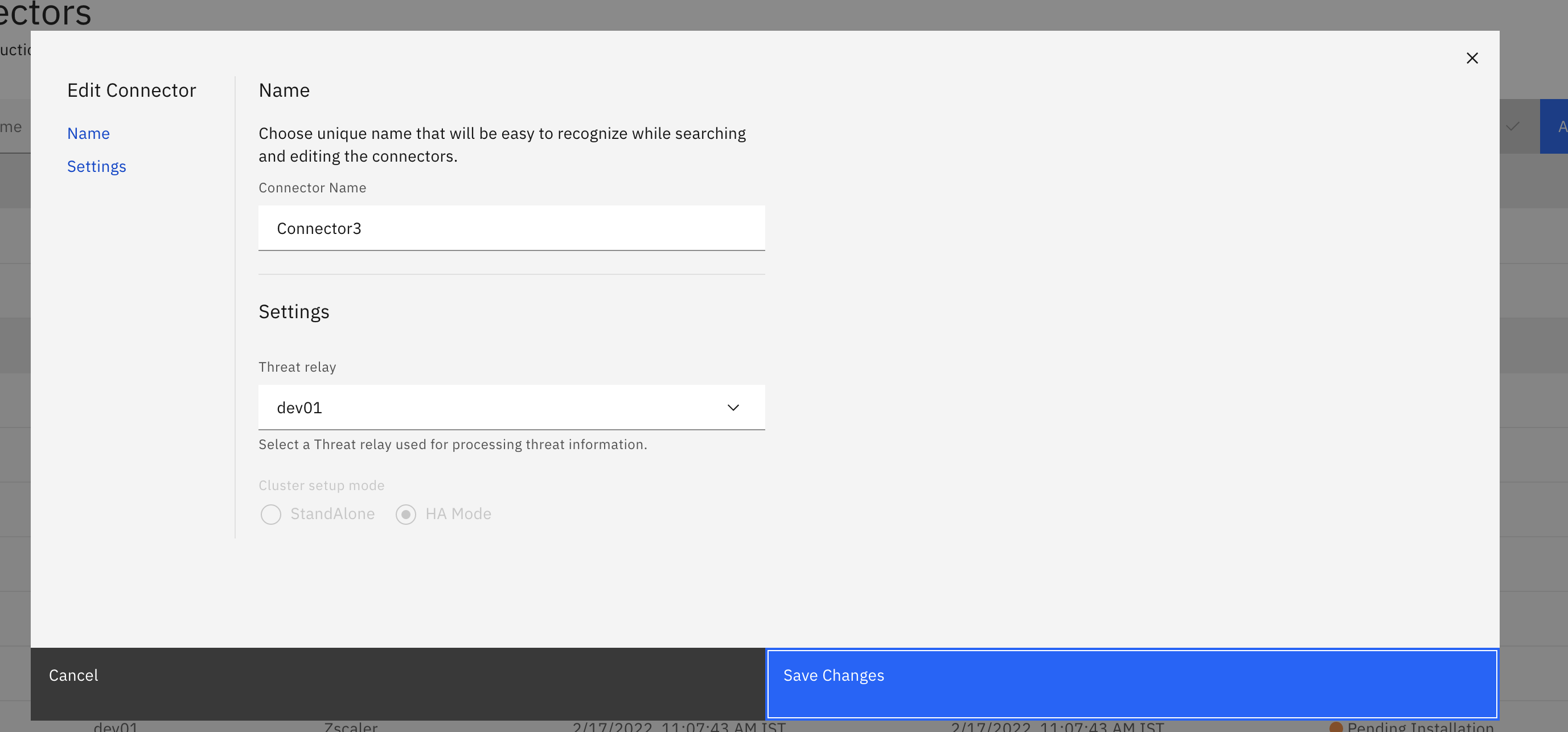
- Configure settings for the threat connector:
- Select the threat relay that processes threat information. Use the relay that is closest to the location where the MaaS360 threat connector is installed.
- Select the installation mode for the threat connector:
- Standalone: Stand-alone mode allows installation of the connector only. (Note: You need the IP address of the host name to configure NSS feeds in the Zscaler portal).
- HA: High availability mode allows multiple installations of a connector. For this mode, you must set up a load balancer and configure the load balancer to split traffic between multiple connector nodes.
- Save the settings.
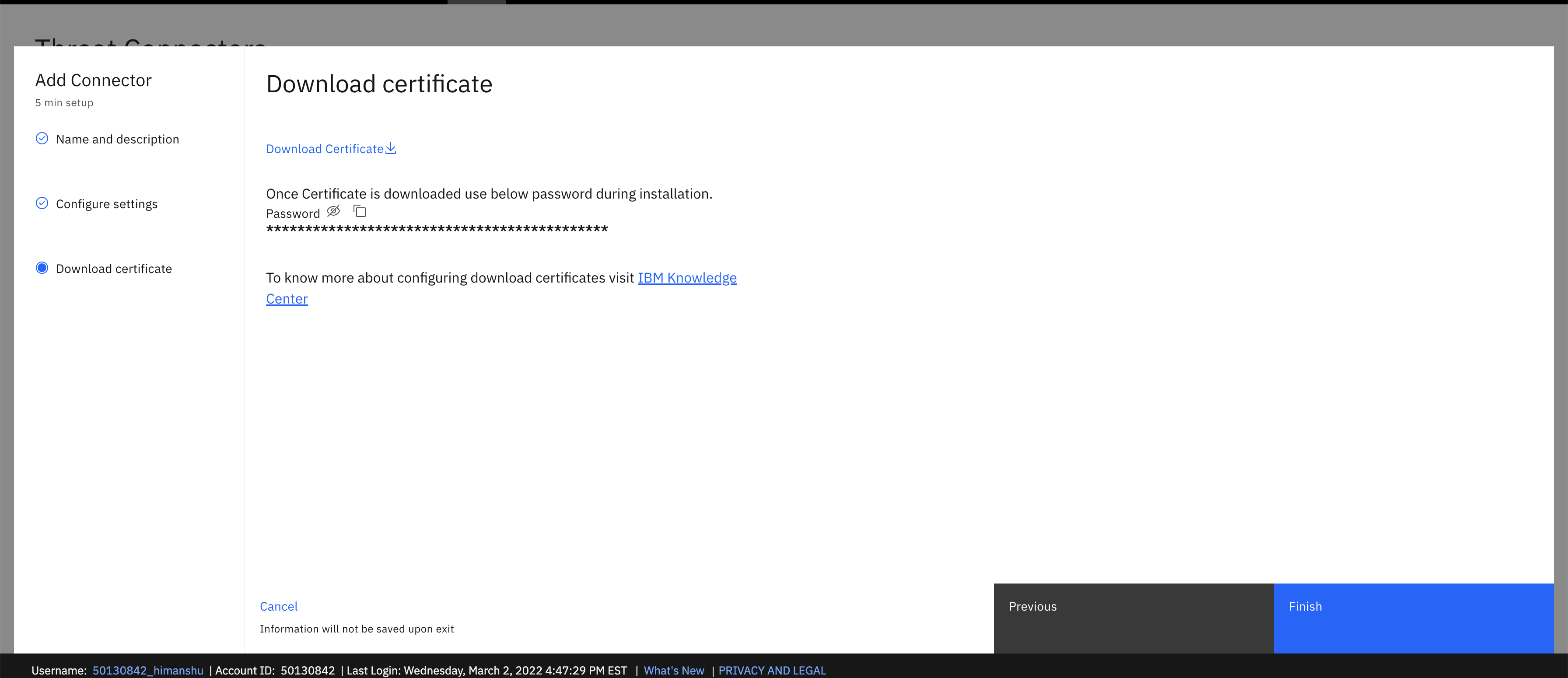
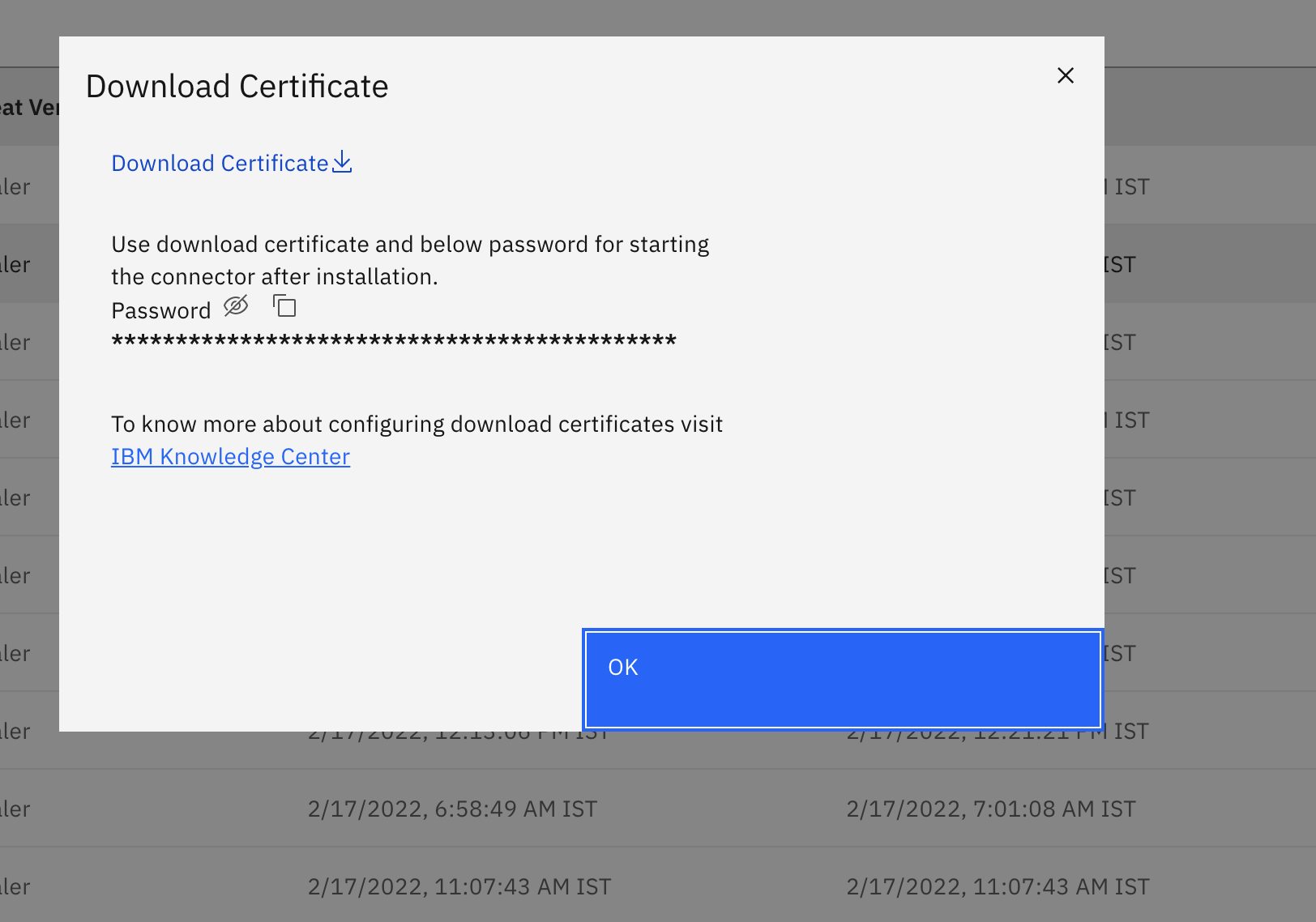
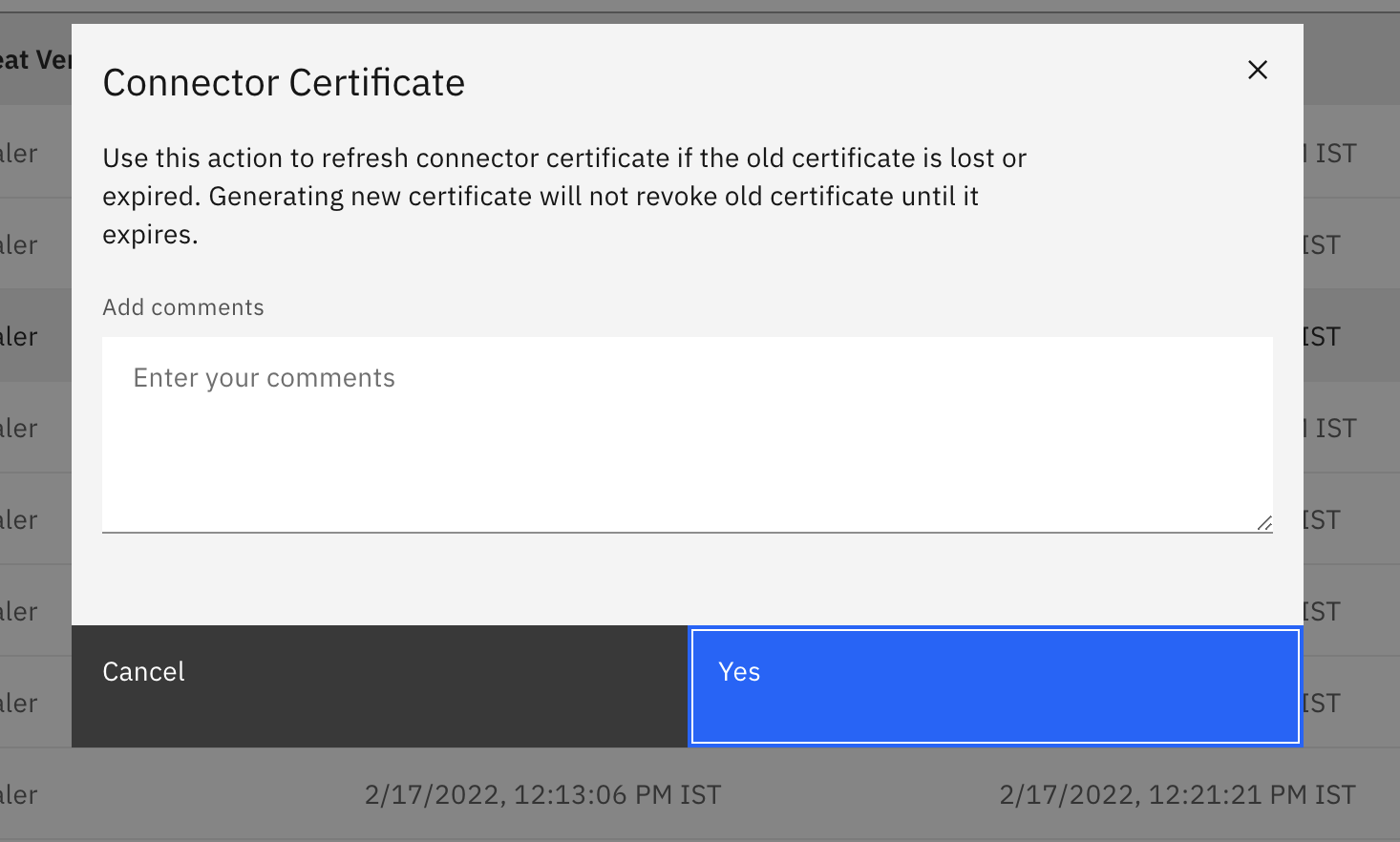
- Download the connector identity certificate and save the certificate password. The connector is displayed in the connector list view. The administrator can edit or modify connectors by selecting the connector and clicking the edit action.
Zscaler uses the Zscaler client connector app to protect user traffic on mobile devices. You can distribute Zscaler connector apps to iOS and Android platforms through MaaS360 application management.
For detailed instructions on how to deploy connector apps through MaaS360 MDM, see the following sites:
Setting up the Zscaler Nanolog streaming service
The Nanolog Streaming Service (NSS) streams security information or other access events detected by Zscaler for further analysis in a customer's SIEM or any other correlation of events. MaaS360 uses the SIEM integration capabilities exposed by Zscaler to consume threat events and the correlation of these events. MaaS360 only supports integration with NSS VM based deployment. MaaS360 can integrate with an existing NSS VM setup or a new VM setup.
Setting up a new NSS VM
Follow the instructions on the Zscaler help page at https://help.zscaler.com/zia/documentation-knowledgebase/analytics/nss/nss-deployment/nss-vm-deployment to set up a new NSS VM.
For an existing NSS VM setup, you must create additional NSS feeds to process security information. After you set up NSS, you must configure the Zscaler threat feeds. For more information about configuring Zscaler threat feeds, see the Configuring the Zscaler threat feed section.
- CPU: 4 core CPUs
- Docker: Install Docker on a Linux VM. If you are using a Windows or macOS machine, you must have a Docker desktop license to run the software.
- Any machine installed with the Docker runtime engine. Follow these instructions to set up Docker on multiple platforms:
- https://docs.docker.com/engine/install/
- Set up on Windows or macOS requires the Docker desktop, which requires a commercial license.
- Any machine installed with the Docker runtime engine. Follow these instructions to set up Docker on multiple platforms:
- Storage: 50 GB of space to save threat information on the disk. This storage must be created as a volume and passed as a parameter to execute the container.
- Network: Allow the following hosts for threat connector integration:
- Allow traffic for *.maas360.com. MaaS360 threat connector uses port 443 for any outbound communication with MaaS360 services.
- The MaaS360 threat connector listens on port 9000 for all threat feeds. Make sure that the NSS VM can access the machine that the threat connector is installed on and can access port 9000.
- Download the Docker image for the MaaS360 threat connector from the MaaS360 Portal at Setup > Threat Connectors. Save the image on the machine or VM where the connector is running.
- Download the identity certificate that runs the connector from either the add connector workflow or by clicking an action and using the download certificate workflow.
- Copy the downloaded certificates to a folder on the machine. In the following example instructions, the folder is named Connector folder where the Docker image is expected to run from.
- Copy the password from the download certificate page for later use.
- Open a terminal and change to the directory where the image and certificates folder are located.
- Use the following command to load the MaaS360 threat connector image:
$ docker load < maas360-threat-connector.tar.gz - Use the following command to verify that the image loaded successfully (the command lists the image; make sure that maas360-threat-connector is part of the listed image):
$ docker images - Use the following command to start running the image:
$ docker run -d --name connector -p 9000:9000 \-v $(path_to_connector_folder):/home/config \
-e CERT_PASSWORD=$(cert_password_from_maas360_portal) \maas360-threat-connector:1.0.0 - Record the IP address and the hostname of the host that the maas360-threat-connector is running on.
- Log in to the Zscaler admin portal and go to the Administration > Nanolog streaming service > NSS Feed section.
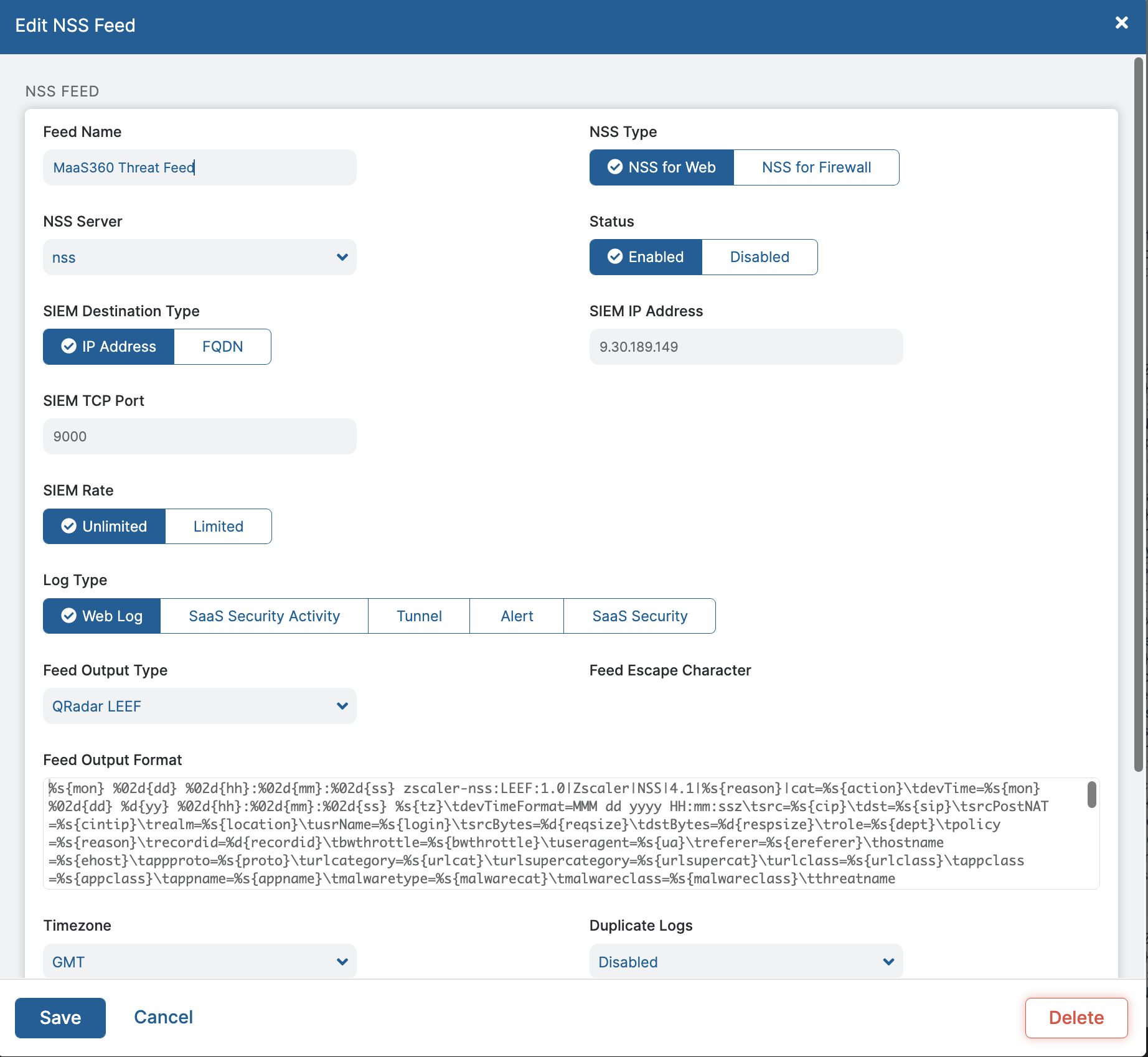
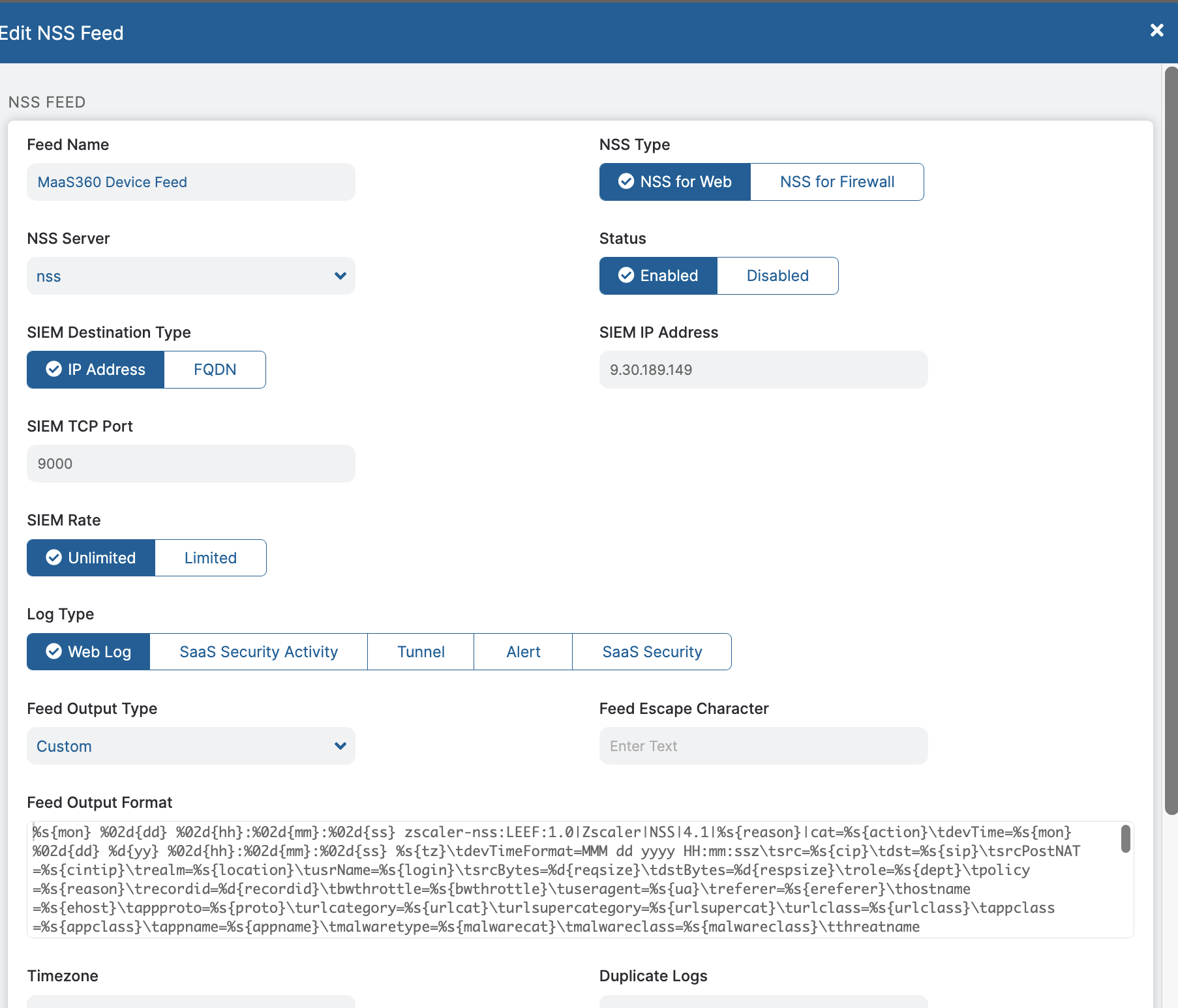
- Click Add NSS Feed and enter the following information:
- Enter the feed name, preferably with the maas360_ prefix to easily identify the feed.
- Select NSS for Web in the NSS Type field.
- Select an NSS server from the drop-down list. You can use a new NSS server setup for MaaS360 integration or an existing NSS server setup in the customer premises.
- Select the SIEM destination type:
- If you select IP address, enter the IP address of the host that the maas360-threat-connector is running on and then enter 9000 as the SIEM TCP port.
- If you select FQDN:
- For stand-alone mode, enter the hostname of the machine that the maas360-threat-connector is executed on.
- For HA mode, enter the load balancer IP address that the maas360-threat-connector is executed on.
- For SIEM Rate, select Unlimited.
- For Log Type, select Web Log.
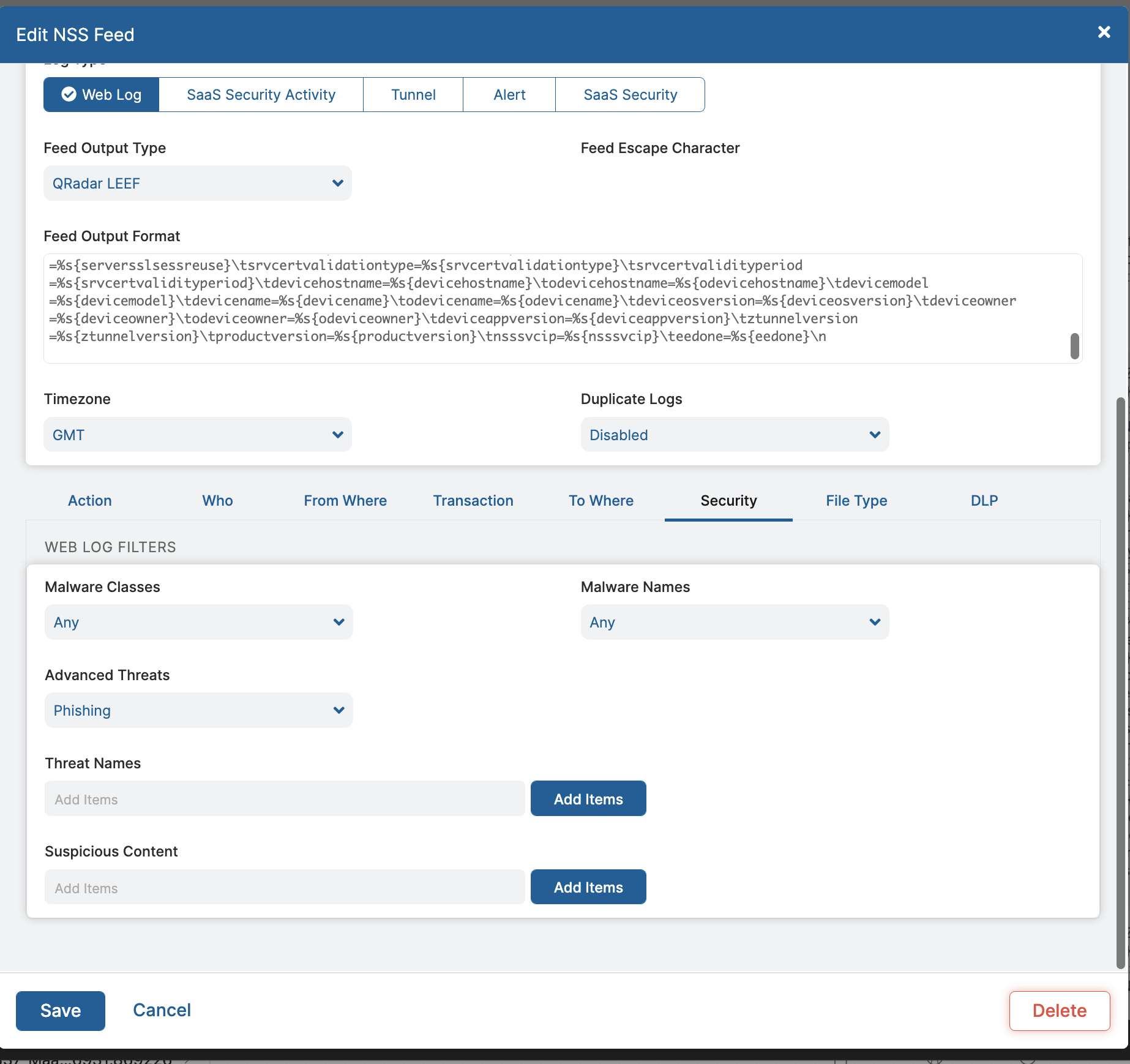
- For Feed Output Type, select QRadar LEEF.
- Enter the following string in the Feed Output Format:
threat_feed_string.txt - Enter the feed time zone in GMT.
- In the Web Log Filters section, go to Security and select All threats in the Advanced Threats section. Use the default settings for the other sections.
- Save the settings.
- Log in to the Zscaler admin portal and go to the Administration > Nanolog streaming service > NSS Feeds section.
- Click Add NSS Feed and enter the following information:
- Enter the feed name, preferably with the maas360_ prefix to easily identify the feed.
- Select NSS for Web in the NSS Type field.
- Select an NSS server from the drop-down list. You can use a new NSS server setup for MaaS360 integration or an existing NSS server setup in the customer premises.
- Select the SIEM destination type:
- If you select IP address, enter the IP address of host that the maas360-threat-connector is running on and then enter 9000 as the SIEM TCP port.
- If you select FQDN:
- For stand-alone mode, enter the hostname of the machine that the maas360-threat-connector is executed on.
- For HA mode, enter the load balancer IP address that the maas360-threat-connector is executed on.
- For SIEM Rate, select Unlimited.
- For Log Type, select Web Log.
- For Feed Output Type, select QRadar LEEF.
- Enter the following string in the Feed Output Format:
device_feed_string.txt - Enter the feed time zone in GMT.
- In the Web Log Filters section, go to Security and select All threats in the Advanced Threats section. Use the default settings for the other sections.
- Save the settings.

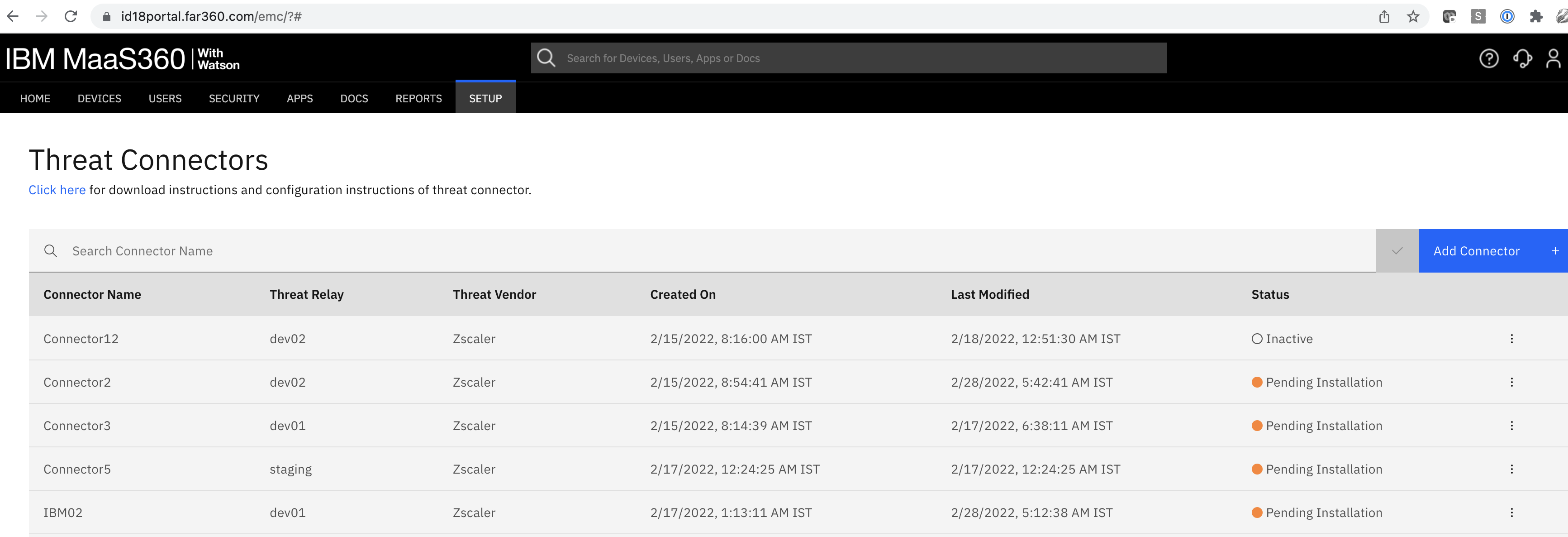
- Connector Name: The name of the connector that is selected from the add connector workflow.
- Threat Relay: The threat relay that was selected from the add connector workflow.
- Threat Vendor: The connector vendor information that threat intelligence is pulled from. (Currently supports Zscaler only)
- Created On: The date and time that the connector was created in the MaaS360 Portal.
- Last Modified: The last date and time the connector settings were edited.
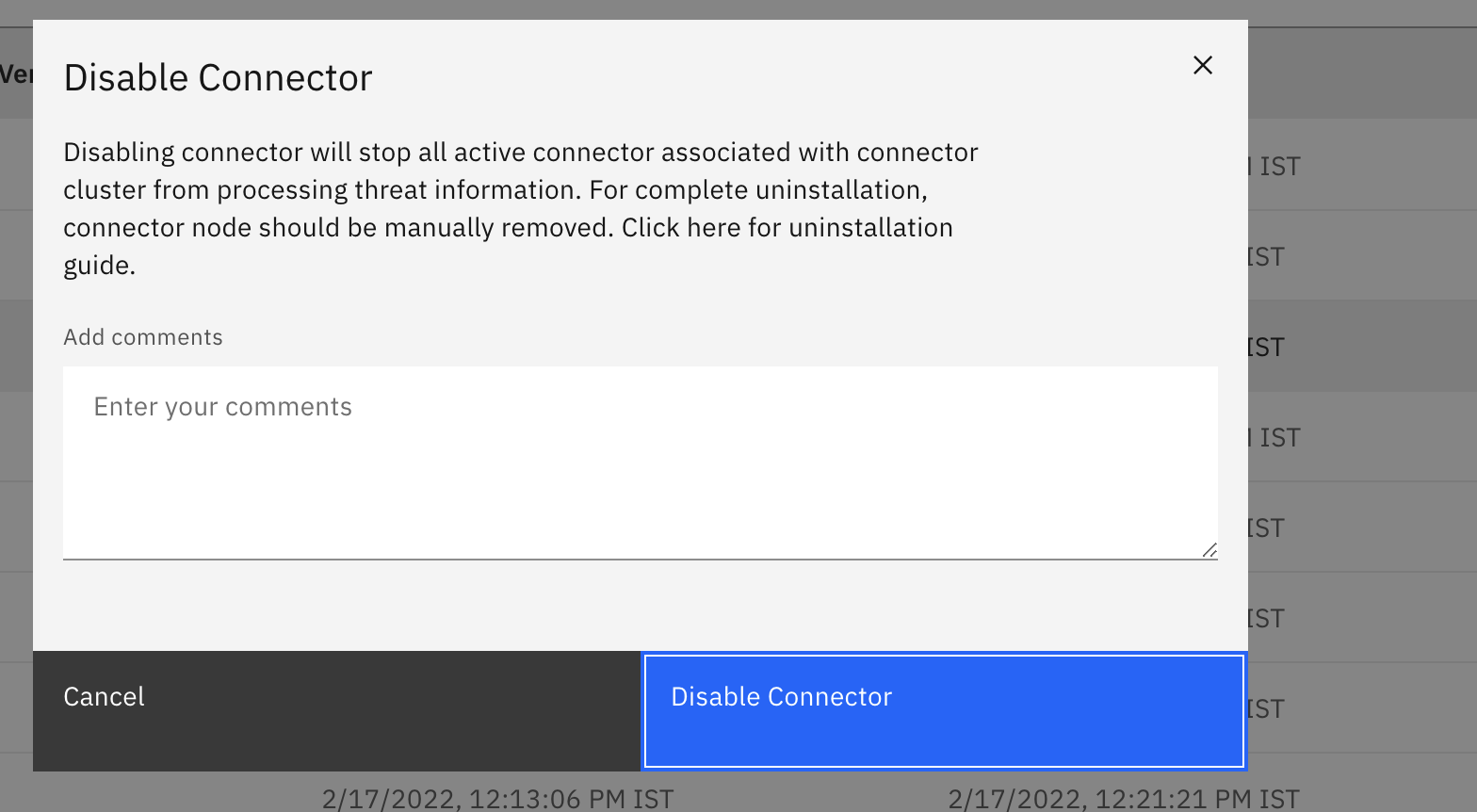
- Status: The exact state of the connector in its lifecycle:
- Pending Installation: The administrator added the connector.
- Online: The administrator installed the connector on a VM and the connector registered with the MaaS360 Portal.
- Offline: The connector is unable to reach MaaS360 after the connector was installed.
- Inactive: The administrator disabled the connector. The connector still pings MaaS360 to check its status, but the connector cannot process threat information.

Use this action to edit settings that are already configured for a connector.
Document Location
Worldwide
Was this topic helpful?
Document Information
Modified date:
07 October 2022
UID
ibm16562691