Security Bulletin
Summary
A privilege escalation vulnerability was addressed in IBM InfoSphere Information Server.
Vulnerability Details
DESCRIPTION: IBM InfoSphere Information Server containers are vulnerable to privilege escalation due to an insecurely configured component.
CVSS Base Score: 8.3
CVSS Temporal Score: See https://exchange.xforce.ibmcloud.com/vulnerabilities/158975 for the current score
CVSS Environmental Score*: Undefined
CVSS Vector: (CVSS:3.0/AV:A/AC:H/PR:N/UI:N/S:C/C:H/I:H/A:H)
Affected Products and Versions
The following products, running on all supported platforms, are affected:
IBM InfoSphere Information Server: version 11.7.1
IBM InfoSphere Information Server on Cloud: version 11.7.1
Remediation/Fixes
| Product | VRMF | APAR | Remediation/First Fix |
| InfoSphere Information Server, Information Server on Cloud |
11.7 | -- |
--Apply IBM InfoSphere Information Server version 11.7.1.0 |
Workarounds and Mitigations
Perform the following steps to secure your environment:
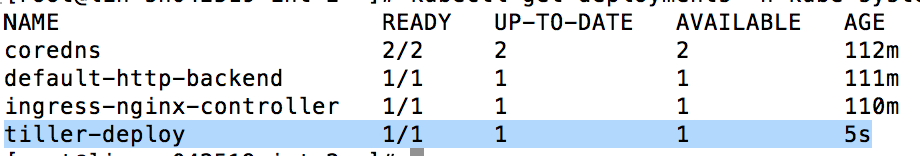
1. List your kube-system namespace
> kubectl get deployments -n kube-system
2. List the pods in your kube-system namespace
> kubectl get deployments -n kube-system
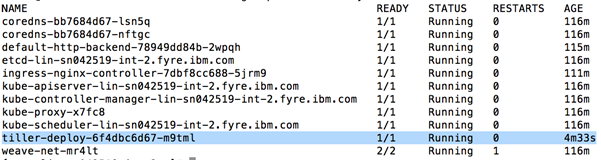
3. Delete the tiller pod
> kubectl delete deployment tiller-deploy --namespace=kube-system
4. Verify that the tiller pod was deleted by examining the output of command
> kubectl get deployments -n kube-system
Verify that helm is working by executing the following command:
> helm list
The output should contain the list of deployed services.
However, if the following error message is displayed:
Error: configmaps is forbidden: User "system:serviceaccount:kube-system:default" cannot list resource "configmaps" in API group "" in the namespace "kube-system"
Execute the following command:
> kubectl patch deploy --namespace kube-system tiller-deploy -p '{"spec":{"template":{"spec":{"serviceAccount":"tiller"}}}}'
After 10 to 20 seconds, again check the output of "helm list" as indicated above.
NOTE:
After making the above changes, if at a later point in time you need to install a patch, you must deploy the tiller pod before installing the patch. Use the following steps:
1. Deploy tiller
> /usr/local/bin/helm init
2. Verify that the tiller POD is created by executing the command
> kubectl get deployments -n kube-system
Get Notified about Future Security Bulletins
References
Change History
06 May 2019: Original version published
24 May 2024: Information Server 11.7.1.1 and later installations are not affected
*The CVSS Environment Score is customer environment specific and will ultimately impact the Overall CVSS Score. Customers can evaluate the impact of this vulnerability in their environments by accessing the links in the Reference section of this Security Bulletin.
Disclaimer
Review the IBM security bulletin disclaimer and definitions regarding your responsibilities for assessing potential impact of security vulnerabilities to your environment.
Internal Use Only
Document Location
Worldwide
Was this topic helpful?
Document Information
Modified date:
24 May 2024
UID
ibm10882626