Security Bulletin
Summary
There is vulnerability in moment-timezone opensource package which affects IBM VM Recovery Manager HA and DR GUI. No impacts to VM Recovery Manager HA and DR cli.
Vulnerability Details
DESCRIPTION: Node.js moment-timezone module could allow a remote attacker to execute arbitrary commands on the system, caused by a command injection vulnerability in the grunt-zdownload.js, data-zdump.js, and data-zic.js scripts. By sending a specially-crafted request, an attacker could exploit this vulnerability to execute arbitrary commands on the system.
CVSS Base score: 7.3
CVSS Temporal Score: See: https://exchange.xforce.ibmcloud.com/vulnerabilities/237819 for the current score.
CVSS Vector: (CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:L)
Affected Products and Versions
| Affected Product(s) | Version(s) |
| VMRM DR | 1.6 |
Remediation/Fixes
Steps followed to fix moment-timezone related security vulnerability issue:
1. Download "dependencyUpdate.ksh" file from path https://aix.software.ibm.com/aix/efixes/security/VMRMDR/VMRM1.6/PVR0355656-MomentTimeZone/
2. Download the moment-time zip file by below given steps.
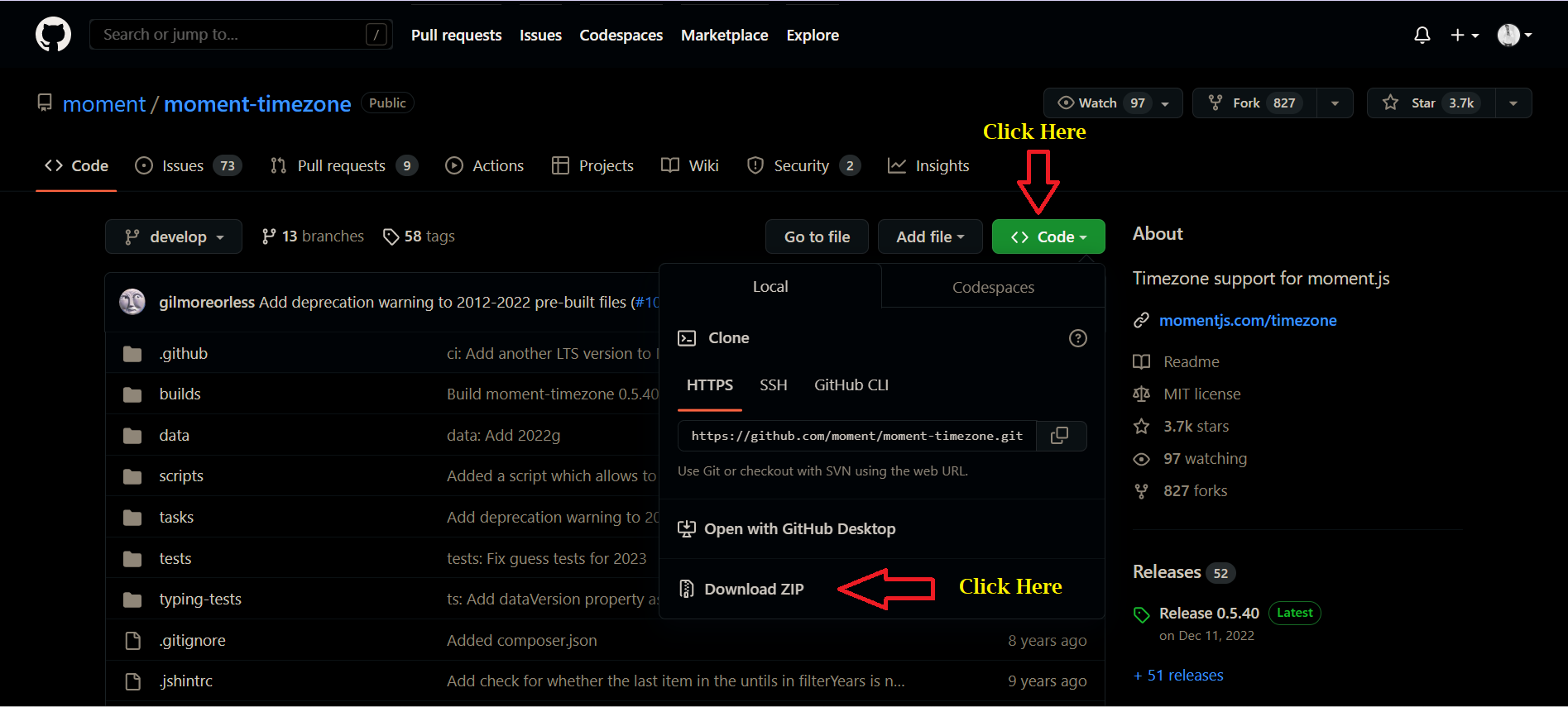
- Open Link https://github.com/moment/moment-timezone
- Click on Code button -> Download ZIP. Screenshot below for reference.
- Keep above downloaded moment-timezone-develop.zip file and dependencyUpdate.ksh in any path like "/tmp" in LPAR. Screenshot for reference.
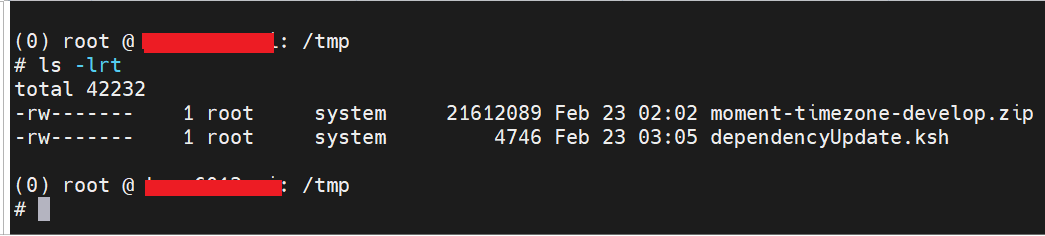
- At the end run command sh ./dependencyUpdate.ksh
Workarounds and Mitigations
Get Notified about Future Security Bulletins
References
Change History
23 Feb 2023: Initial Publication
*The CVSS Environment Score is customer environment specific and will ultimately impact the Overall CVSS Score. Customers can evaluate the impact of this vulnerability in their environments by accessing the links in the Reference section of this Security Bulletin.
Disclaimer
According to the Forum of Incident Response and Security Teams (FIRST), the Common Vulnerability Scoring System (CVSS) is an "industry open standard designed to convey vulnerability severity and help to determine urgency and priority of response." IBM PROVIDES THE CVSS SCORES ""AS IS"" WITHOUT WARRANTY OF ANY KIND, INCLUDING THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. CUSTOMERS ARE RESPONSIBLE FOR ASSESSING THE IMPACT OF ANY ACTUAL OR POTENTIAL SECURITY VULNERABILITY. In addition to other efforts to address potential vulnerabilities, IBM periodically updates the record of components contained in our product offerings. As part of that effort, if IBM identifies previously unidentified packages in a product/service inventory, we address relevant vulnerabilities regardless of CVE date. Inclusion of an older CVEID does not demonstrate that the referenced product has been used by IBM since that date, nor that IBM was aware of a vulnerability as of that date. We are making clients aware of relevant vulnerabilities as we become aware of them. "Affected Products and Versions" referenced in IBM Security Bulletins are intended to be only products and versions that are supported by IBM and have not passed their end-of-support or warranty date. Thus, failure to reference unsupported or extended-support products and versions in this Security Bulletin does not constitute a determination by IBM that they are unaffected by the vulnerability. Reference to one or more unsupported versions in this Security Bulletin shall not create an obligation for IBM to provide fixes for any unsupported or extended-support products or versions.
Document Location
Worldwide
Was this topic helpful?
Document Information
Modified date:
24 February 2023
UID
ibm16957710