Technical Blog Post
Abstract
Configuring Application Server Security with Decision Optimization Server
Body
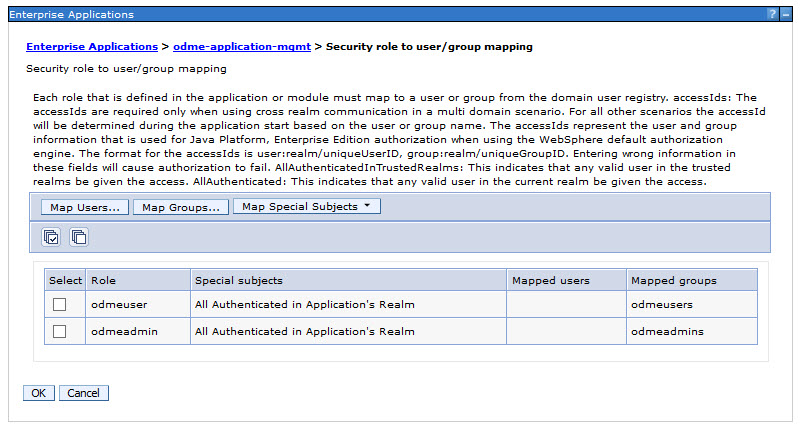
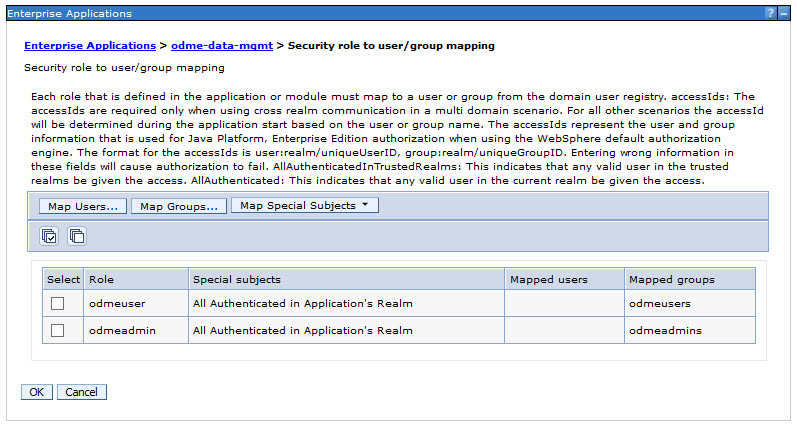
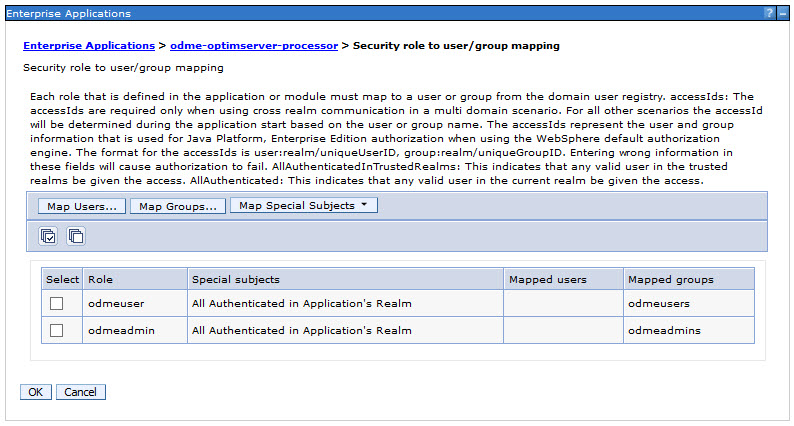
When deployed into the enterprise as a production system, it replaces the default file-based configuration. In this case, the roles mapping to the EAR modules must be matched in the new security definition. Below are screenshots for each application showing the mappings.
[{"Business Unit":{"code":"BU059","label":"IBM Software w\/o TPS"},"Product":{"code":"SSLKT6","label":"IBM Maximo Asset Management"},"Component":"","Platform":[{"code":"PF025","label":"Platform Independent"}],"Version":"","Edition":"","Line of Business":{"code":"LOB59","label":"Sustainability Software"}}]
UID
ibm11113723