Release Notes
Abstract
Microsoft announced the deprecation of Basic Authentication for legacy protocols: Exchange Active Sync (EAS), Post Office Protocol (POP), Internet Message Access Protocol (IMAP), and Remote PowerShell (RPS) in Exchange Online. Modern Authentication is the only path forward for the existing Exchange Online customers that use Basic Authentication.
Content
Basic Authentication vs Modern Authentication
Basic Authentication uses a username and password, which is transmitted from the requesting application each time access requests are made to a service, for example, Exchange Online, Salesforce, or Box. The username and password used to authenticate are often stored on the requesting device, for example a browser, making it easier for the attackers to capture and reuse those stolen credentials against other services.
Modern Authentication is based on ADAL (Active Directory Authentication Library) and OAuth 2.0 protocols. The term “Modern Authentication” describes Federated Identity Management. Federated Identity Management moves away from username and passwords being directly transmitted from the requester to the service. It instead leverages token based requests that are generated by an Identity Providers (IdP), for example IBM Verify, Microsoft Azure AD, Okta, and Ping. IdP's transmit these tokens to the service from the requesting user or device. The tokens are stored at the device rather than a username and password. Multifactor Authentication (MFA), Passwordless, and Single Sign-On (SSO), are all components of Modern Authentication.
Impact
New and existing client applications that use any of the legacy protocols cannot connect to Exchange Online (Office 365 mailboxes or endpoints) that use Basic Authentication. The client applications that use Modern Authentication are not affected. This article does not apply to Exchange on-premise customers.
Timelines
Microsoft will be deprecating Basic Authentication in all tenants on 1 October 2022.
How do you know whether you are still using Basic Authentication?
The quickest way to check is within the MaaS360 portal in the email portion of security policies to see whether Modern Authentication is enabled. You can also determine whether Basic Authentication is being used based on the screen provided for authentication of the requesting application’s interface. Modern authentication redirects to your IdP’s external login screen while Basic Authentication asks for password input locally.
Device examples:
| Basic Authentication Prompt | Modern Authentication Prompt |
|---|---|
 |
 |
Policy examples:
Android MDM ActiveSync Policy has Authentication Mode set to Basic.

iOS MDM ActiveSync Policy has Enable Oauth Authentication set to No.

WorkPlace Persona Policy for Secure Mail has Enable SSO checkbox cleared.

Note: Publishing changes suggested to the mail policy requires users to reauthenticate.
Native email configured through MaaS360 MDM policies
Legacy Device Administrator
ActiveSync policies no longer function on non-Android Enterprise devices. Customers must either migrate to Android Enterprise or configure the Secure Mail application through Persona policies.
Android Enterprise
- From the MaaS360 Portal, select Security > Policies.
- Open an Android MDM policy and navigate to Android Enterprise Settings > ActiveSync.
- In the Authentication Mode setting, select Modern.

- Save and publish the policy.
Note: Supervised devices on iOS 15 and below need toggle Allow Account Modification to Yes under Supervised Settings > Restrictions & Network. Supervised devices on iOS 16 and higher don't require Allow Account Modification set to Yes if MaaS360 is pushing the mail payload.
- From the MaaS360 Portal, select Security > Policies.
- Open an iOS MDM policy and navigate to Device Settings > ActiveSync.
- Select the Enable OAuth Authentication checkbox. Leave the OAuth Sign-in URL and the OAuth Token Request URL blank.
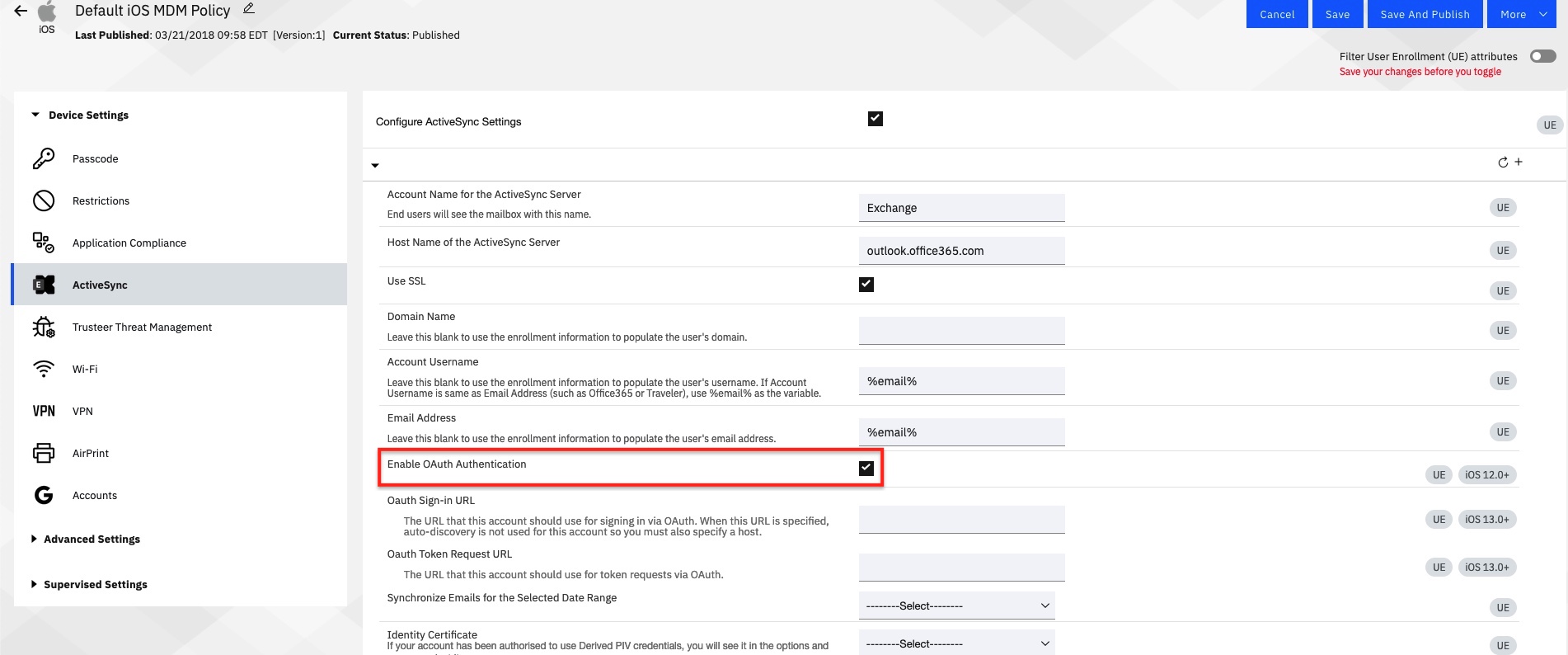
- Save and publish the policy.
Note: To use Office365 Modern Authentication with Android Secure Mail the policy must be as follows:
Account Username: %email% (or %upn% if the UPN for login to Office365 and the UPN is different from the user email)
Email Address: Can be left blank or leverage policy wildcards
Domain Name: Must be blank
- From the MaaS360 Portal, select Security > Policies.
- Open a Workplace Persona policy and navigate to .
- Select Office 365 for Mail Server and then select Enable SSO. The App Client ID section is displayed.
- Enter the application (client) ID in the App Client ID section. For more information about the application client ID, see Registering MaaS360 app in the Azure AD tenant.
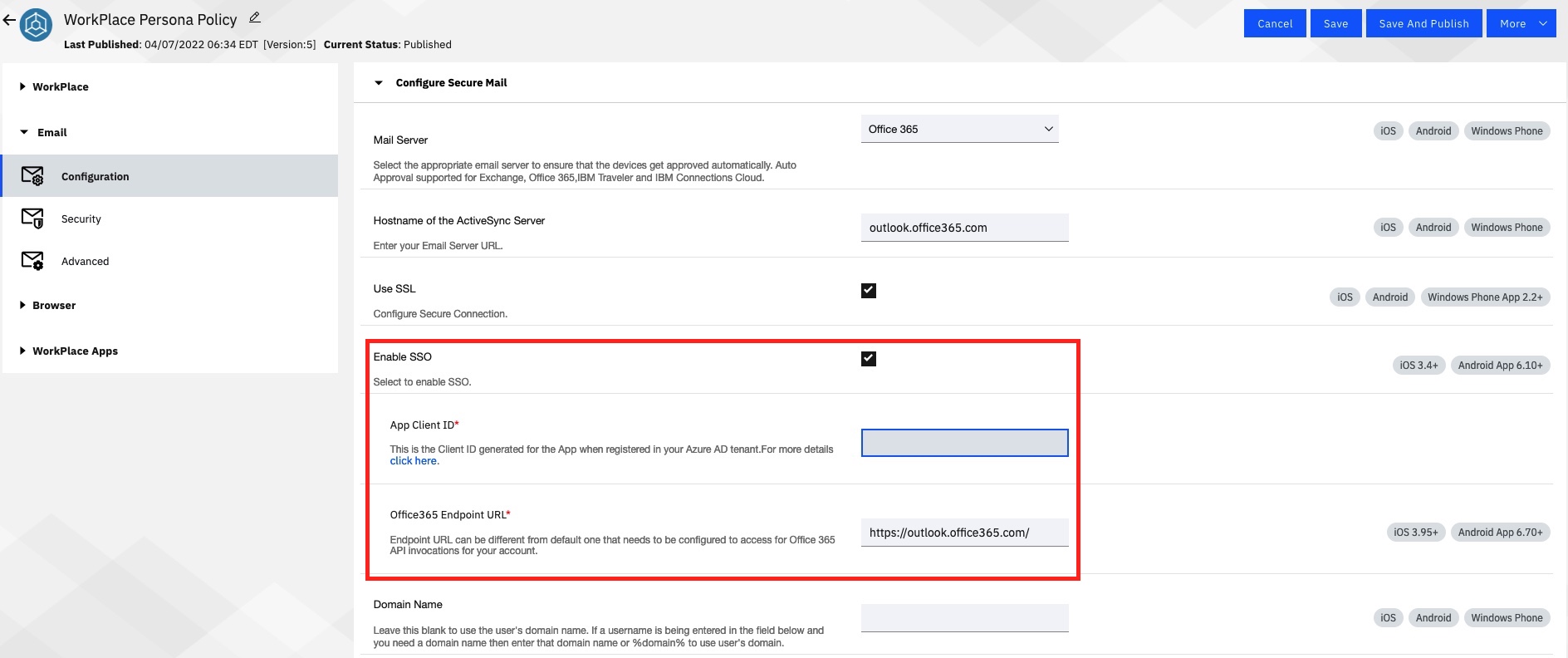
Note: Applicable for existing app configurations. New app configurations leverage the Add configuration workflow.
Android
- From the MaaS360 Portal, select Apps > App Configurations.
- Select the three dots on the right and choose View.
- Select Edit in the lower right and scroll down to account type.
- In the account type field, enter ModernAuth and publish the app configuration.

iOS
- From the MaaS360 Portal, select Apps > App Configurations.
- Select the three dots on the right and choose View.
- Select Edit in the lower right and locate Account Type.
- From the Account Type drop-down, select Office 365 or Hybrid (Modern Authentication) and publish the app configuration.

Exchange ActiveSync Module
Note: Requires Cloud Extender Exchange ActiveSync 2.106.650 modules. Contact MaaS360 support for the Exchange ActiveSync 2.106.650 modules.
Customers that use the Cloud Extender Exchange ActiveSync module must follow the instructions found here to switch to Modern Authentication.
Email Notification Module
Customers that use the Cloud Extender Email Notification module must follow the instructions found here to switch to Modern Authentication.
Was this topic helpful?
Document Information
Modified date:
26 October 2022
UID
ibm16615243