How To
Summary
Using kerberos authentication to Hive/Impala HOWEVER they need to ensure that the user that is running a report has their
credentials passed down to the DB , TGT (Ticket Granting Ticket).
Objective
The user is defined and defined only once, and allows access to other users/projects that will be granted read access to the My_DATA_HUB tables per project. It is the user/pwd that will change only each time a new connection to the My_DATA_HUB kerberos databases is defined.
Steps
ACTION TO BE CARRIED OUT ON ALL DISPATCHERS
1- Make sure you are using the Unrestricted version of the JCE for Cognos. (https://www.ibm.com/support/knowledgecenter/SSEP7J_11.1.0/com.ibm.swg.ba.cognos.inst_cr_winux.doc/c_adv_config_change_jre_version.html)
/applis/cognos/dispatcher/ibm-jre/jre/lib/security/policy/unlimited
-rwxr-xr-x. 1 cscognosbi cscognosbi 2195 Mar 19 16:35 local_policy.jar
-rwxr-xr-x. 1 cscognosbi cscognosbi 2184 Mar 19 16:35 US_export_policy.jar
-rwxr-xr-x. 1 cscognosbi cscognosbi 2184 Mar 19 16:35 US_export_policy.jar
2- Created krb5.conf file, it must be placed in /etc as well as in directory <App>/jre/lib/security (this one will be specific for your authentication source)
krb5.conf by default /etc/krb5.conf copy to /applis/cognos/dispatcher/ibm-jre/jre/lib/security
krb5.conf by default /etc/krb5.conf copy to /applis/cognos/dispatcher/ibm-jre/jre/lib/security
**** For all dispatchers
3- Copy Impala driver
3- Copy Impala driver
https://www.cloudera.com/downloads/connectors/impala/jdbc/2-6-15.html on each dispatchers ../drivers/ImpalaJDBC42.jar
JDBC42 version 2.6.15.1017 because IBM-JRE_version=8.0.5.35 cf https://docs.cloudera.com/documentation/other/connectors/impala-jdbc/latest/Cloudera-JDBC-Driver-for-Impala-Install-Guide.pdf
- copy HIVE driver ../drivers/hive-jdbc-2.1.0.2.6.2.1-1-standalone.jar
4- Hive DB connection use : ibmcognos.subcode=HIVE2;ibmcognos.authentication=java_krb5;
and "ibmcognos.authentication=java_krb5" in the DB connection, this indicates that a kerberos method is used :
^User ID:^?Password:;LOCAL;JDBC;URL=jdbc:hive2://xx.customer.xx:10000/DbName;principal=hive/xx.customer.xx@domain.com;hive.execution.engine=tez;DRIVER_NAME=org.apache.hive.jdbc.HiveDriver;ibmcognos.subcode=HIVE2;ibmcognos.authentication=java_krb5;
IMPALA DB connection :
^User ID:^?Password:;LOCAL;JDBC;URL=jdbc:impala://xx.customer.xx:21000/DbName;AuthMech=1;KrbHostFQDN=xx.customer .xx;KrbRealm=domain.com;KrbServiceName=impala;DRIVER_NAME=com.cloudera.impala.jdbc4.Driver;ibmcognos.authentication=java_krb5 ;
Ps : Take attention to online documentation below, "Related Information" part, section "Using Kerberos authentication without single sign-on"
Additional Information
Creating a Kerberized connection to Apache Hive from Cognos Analytics 11.1.x from Red Hat Enterprise Linux.
**Disclaimer: these steps were tested and validated in Cognos Analytics 11.1.5 against Apache Hive 3.1.0.3.1.4.0-315 using Hive JDBC driver 2.1.0.2.6.2.1-1.
Steps to create connection :
1) Generate an appropriate krb5.conf file; the documentation available at https://web.mit.edu/kerberos/krb5-1.12/doc/admin/conf_files/krb5_conf.html provides the information you should need in coordination with your LDAP admin.
A simple example of a krb5.conf file :
1) Generate an appropriate krb5.conf file; the documentation available at https://web.mit.edu/kerberos/krb5-1.12/doc/admin/conf_files/krb5_conf.html provides the information you should need in coordination with your LDAP admin.
A simple example of a krb5.conf file :
| [libdefaults] default_realm = ATHENA.MIT.EDU default_tkt_enctypes = des3-hmac-sha1 des-cbc-crc default_tgs_enctypes = des3-hmac-sha1 des-cbc-crc dns_lookup_kdc = false dns_lookup_realm = false [realms] ATHENA.MIT.EDU = { kdc = kerberos.mit.edu kdc = kerberos-1.mit.edu kdc = kerberos-2.mit.edu:750 admin_server = kerberos.mit.edu master_kdc = kerberos.mit.edu default_domain = mit.edu } EXAMPLE.COM = { kdc = kerberos.example.com kdc = kerberos-1.example.com admin_server = kerberos.example.com } [domain_realm] .mit.edu = ATHENA.MIT.EDU mit.edu = ATHENA.MIT.EDU [capaths] ATHENA.MIT.EDU = { EXAMPLE.COM = . } EXAMPLE.COM = { ATHENA.MIT.EDU = . } [logging] kdc = SYSLOG:INFO admin_server = FILE=/var/kadm5.log |
2) Ensure that you have the krb5.conf file created in step 1 placed in ( 2 different cases):
- /etc/ directory for external Java.
- <installation>/ibm-jre/jre/lib/security/ directory for Java from Cognos Analytics.
3) Leveraging product documentation (https://www.ibm.com/support/knowledgecenter/en/SSEP7J_11.1.0/com.ibm.swg.ba.cognos.inst_cr_winux.doc/t_ig_verifyjdbccaps.html), ensure that the driver in question supports kerberized connections. You should expect to see an output similar to this:
HIVE :
IMPALA :
4) Create the data source connection inside of Cognos Administration.
Use the following “Connection properties:” values for HIVE : ibmcognos.subcode=HIVE2;ibmcognos.authentication=java_krb5;
Use the following “Connection properties:” values for IMPALA : ibmcognos.authentication=java_krb5;
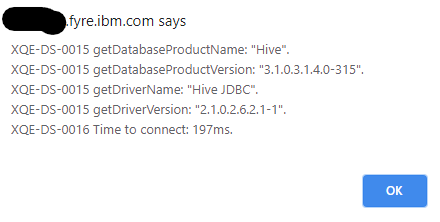
5) Test the data source connection. As long as you are using the correct UserName and Password, you should get a result similar to this:

6) Clicking on the “Succeeded” link will give you the relevant information from the connection (e.g. database version, driver version):
HIVE
IMPALA

You can validate that you are passing a username and password by changing the password to a known incorrect password. In such cases, you will get the following error message:
Related Information
Document Location
Worldwide
[{"Line of Business":{"code":"LOB10","label":"Data and AI"},"Business Unit":{"code":"BU059","label":"IBM Software w\/o TPS"},"Product":{"code":"SSTSF6","label":"IBM Cognos Analytics"},"ARM Category":[{"code":"a8m50000000Cl6OAAS","label":"Installation and Configuration->Authentication"}],"ARM Case Number":"TS004003799","Platform":[{"code":"PF016","label":"Linux"}],"Version":"All Version(s)"}]
Was this topic helpful?
Document Information
Modified date:
17 March 2021
UID
ibm16415075